Beef Up Your Network Security With These Physical Protection Tips
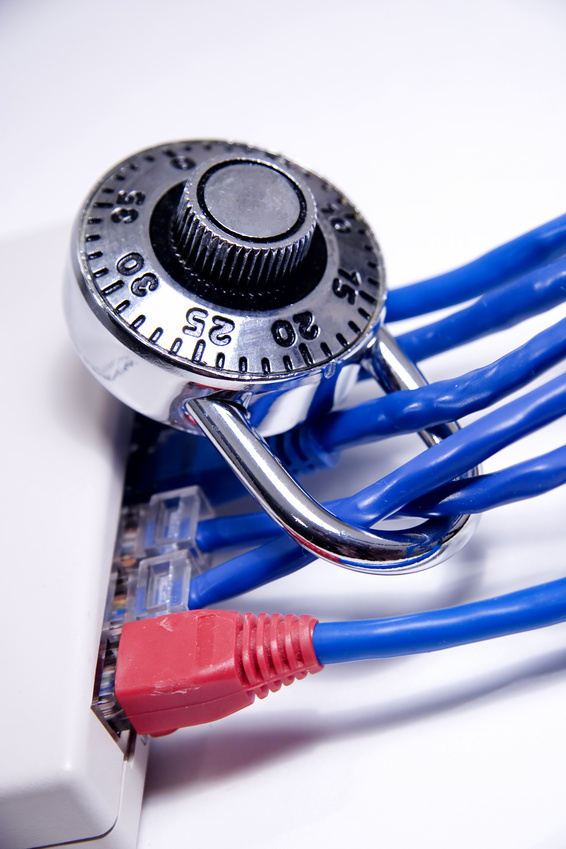
It’s correct to focus on firewalls, virus protection, and other software measures to protect your company’s data. Hackers and viruses often try to destroy or steal information through virtual means.
However, consider what would it would mean to your company if a laptop full of your customer’s credit card numbers is stolen from an employee’s unlocked car, or someone looking through your office windows sees a secretary type employee Social Security numbers into your company database. Physical protection is also an important component of network security.
Start by recording the location of any company-owned devices used to access information, including desktops, laptops, tablets, and smartphones. Keep track of who is using the asset, why he or she has it, and where it goes if taken outside the office. This is particularly important for devices that are obsolete or no longer being used. These are often forgotten under a desk or left in unlocked drawers. They should inside a locked cabinet within a locked room, such as where your servers are located.
Give keys to the secure room only to yourself and a few trusted employees. Anyone who requires access or who must borrow a device must go through these individuals. In addition, cameras inside the room and in the corridors leading to it act as a further security strategy. Store the video recorded by these cameras in two locations: onsite for easy access and offsite to prevent tampering.
For more information on how to implement solutions for total network security, please contact us.

